

Getty Photographs
Almost 71 million distinctive credentials stolen for logging into web sites equivalent to Fb, Roblox, eBay, and Yahoo have been circulating on the Web for at the very least 4 months, a researcher stated Wednesday.
Troy Hunt, operator of the Have I Been Pwned? breach notification service, stated the huge quantity of information was posted to a widely known underground market that brokers gross sales of compromised credentials. Hunt stated he usually pays little consideration to dumps like these as a result of they merely compile and repackage beforehand printed passwords taken in earlier campaigns.
Not your typical password dump
Some obtrusive issues prevented Hunt from dismissing this one, particularly the contents indicating that almost 25 million of the passwords had by no means been leaked earlier than:
- 319 recordsdata totaling 104GB
- 70,840,771 distinctive e mail addresses
- 427,308 particular person HIBP subscribers impacted
- 65.03 p.c of addresses already in HIBP (primarily based on a 1,000 random pattern set)
“That final quantity was the actual kicker,” Hunt wrote. “When a 3rd of the e mail addresses have by no means been seen earlier than, that is statistically vital. This is not simply the typical assortment of repurposed lists wrapped up with a brand-new bow on it and handed off as the subsequent huge factor; it is a vital quantity of new information. If you have a look at the above discussion board submit the information accompanied, the purpose why turns into clear: it is from ‘stealer logs’ or in different phrases, malware that has grabbed credentials from compromised machines.”
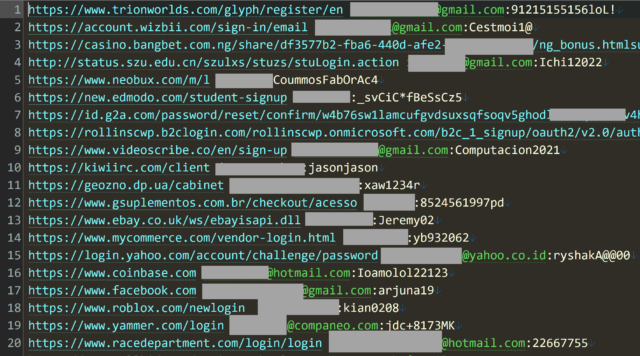
A redacted picture that Hunt posted displaying a small pattern of the uncovered credentials indicated that account credentials for a range of websites had been swept up. Websites included Fb, Roblox, Coinbase, Yammer, and Yahoo. Consistent with the declare that the credentials had been collected by a “stealer”—malware that runs on a sufferer’s gadget and uploads all person names and passwords entered right into a login web page—the passwords seem in plaintext. Account credentials taken in web site breaches are virtually all the time cryptographically hashed. (A tragic apart: Most of the uncovered credentials are weak and would simply fall to a easy password dictionary assault.)
Have I Been Pwned?
Information collected by Have I Been Pwned signifies this password weak point runs rampant. Of the 100 million distinctive passwords amassed, they’ve appeared 1.three billion occasions.
“To be truthful, there are cases of duplicated rows, however there’s additionally an enormous prevalence of individuals utilizing the identical password throughout a number of totally different providers and fully totally different individuals utilizing the identical password (there are a finite set of canine names and years of delivery on the market…),” Hunt wrote. “And now greater than ever, the influence of this service is completely enormous!”
Hunt confirmed the authenticity of the dataset by contacting individuals at some of the listed emails. They confirmed that the credentials listed there have been—or at the very least as soon as had been—correct. For added assurance, Hunt additionally checked a pattern of the credentials to see if the e mail addresses had been related to accounts on the affected web sites. All of them did. Some of Hunt’s customers reported that the passwords gave the impression to be legitimate as of 2020 or 2021. No matter the date of the passwords, it stands to purpose that except they’ve been up to date, they continue to be legitimate. The underground market submit promoting the dataset stated it got here from a breach dubbed naz.api that had been donated to a special website earlier.
Hunt stated that a big proportion of the credentials got here not from stealer malware as claimed, however from credential stuffing, a type of account-hijacking assault that collects giant numbers of stolen account credentials from earlier breaches. Hunt stated credential stuffing sources defined how a password he used “pre-2011” landed in the dump.
“Some of this information doesn’t come from malware and has been round for a big interval of time,” he wrote. “My very own e mail deal with, for instance, accompanied a password not used for nicely over a decade and didn’t accompany an internet site indicating it was sourced from malware.”
Making passwords secure
There are dozens of helpful primers on-line explaining how you can correctly safe accounts. The 2 foremost substances to account safety are: (1) selecting robust passwords and (2) protecting them out of the sight of prying eyes. This implies:
- Creating a protracted, randomly generated password or passphrase. These passcodes must be at the very least 11 characters for passwords and for passphrases at the very least 4 phrases randomly chosen from a dictionary of no fewer than 50,000 entries. Bitwarden, a free, open-source password supervisor is an efficient alternative and an effective way for much less skilled individuals to get began. As soon as a password is created, it must be saved in the password-manager vault.
- Stopping robust passwords from being compromised. This entails not getting into passwords into phishing websites and protecting gadgets free of malware.
- Use two-factor authentication, ideally with a safety key or authenticater app, every time attainable. This doubly applies to defending the password supervisor with 2FA.
- Higher but, use passkeys, a brand new, industry-wide authentication commonplace that is proof against theft by means of stealer apps and credential phishing.
It’s additionally a good suggestion to both create an account with Have I Been Pwned? or periodically enter e mail addresses into the website search field to examine if they seem in any breaches. To stop abuse of the search, the website doesn’t log entered e mail addresses and no corresponding passwords are loaded with password information saved on the website. Have I Been Pwned additionally accepts a single e mail deal with at a time, besides in sure circumstances. You could find extra on the service and the safety of utilizing it right here.
Have I Been Pwned additionally permits customers to look its database for particular passwords. Extra about k-anonymity and different measures Hunt makes use of to forestall password publicity and abuse of his service is right here.
This submit has been up to date to right inferences about how Hunt’s password ended up in the dataset.